Topic
This Knowledge Base article explains why security scanning tools may report false vulnerabilities when analyzing Nintex RPA Central. Some tools only read the initial HTTP 401 response and incorrectly flag it as a vulnerability.
Instructions
If your security teams reported a potential vulnerability after seeing a 401 response when scanning the Nintex RPA Central URL. This caused concerns that HSTS headers were missing or that authentication was failing.
Please note that some scanning tools do not proceed with NTLM checks and only record the first response. This results in a *false negative* where the system appears insecure even though it is functioning correctly.
We use HSTS and HSTS response headers. Please follow the steps below and share the results with your security team so they can validate that this is not a security vulnerability.
Open RPA Central from the machine itself:
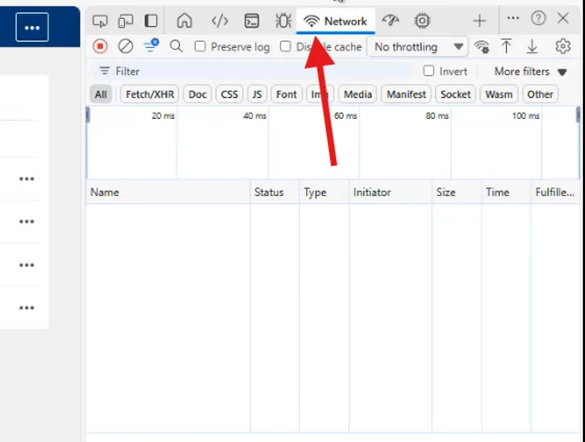
Press F12 on Edge (or right-click → Inspect), then click on the Network tab as shown below, and refresh the page:
What this does is call our actual API, which is the backend service. It calls an endpoint on the API, and you can check the response headers of that call.
We use HSTS as one of the response headers for security. You can verify this under Jobbotflows and Bots, as shown in the image:
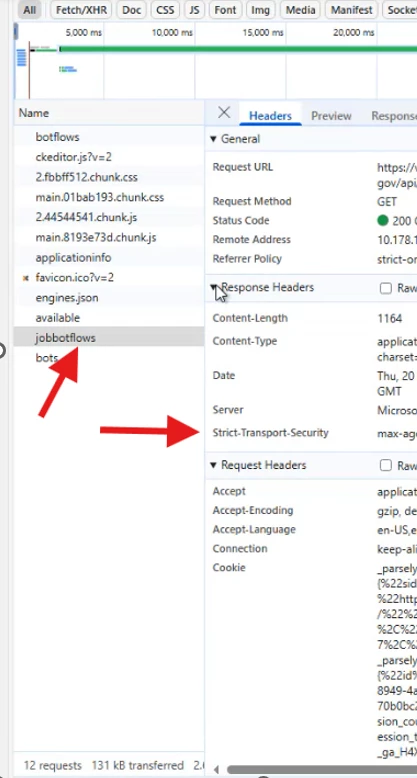
Our application uses HSTS, and you must pass these findings to your security team so they can validate and clear the flagged vulnerability on their side. This is essentially a sanity check.
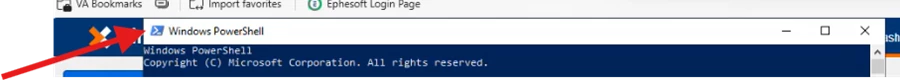
Please run the script below in PowerShell and share the results with your security team as well. The machine must have Windows PowerShell; CMD will not run this command.:
Script- Please use your RPAC URL where it says Your RPAC URL:
$response = Invoke-WebRequest -Uri "Your RPAC URL” -UseDefaultCredentials -UseBasicParsing
Write-Host "Status Code:" $response.StatusCode
Write-Host "`n=== Response Headers ===" -ForegroundColor Cyan
$response.Headers | Format-Table -AutoSize
Write-Host "`n=== HSTS Header Check ===" -ForegroundColor Yellow
if ($response.Headers['Strict-Transport-Security']) {
Write-Host "✓ HSTS Found: " $response.Headers['Strict-Transport-Security'] -ForegroundColor Green
} else {
Write-Host "✗ HSTS NOT Found" -ForegroundColor Red
}
The script validates the web request and analyzes the response headers. If HSTS is present, the script will confirm it. It uses your currently logged-in Windows user, so no credentials need to be entered.
RPA Central is a Windows service that is self-hosted as a web application. It has a web interface that you interact with.
Even if the domain is correct, entering an incorrect path never interacts with our servers. You will always get a 401 because we don’t handle invalid paths. Since it is not an IIS-hosted application, it communicates only through its own self-hosted service.
The next part is the negotiate call, which is likely what your security team is using to run their scan. This will show what they see and why the issue was flagged.
Run this command in PowerShell: curl.exe -I --negotiate -u : YOUR RPAC URL
This uses curl, which comes with Windows 10, and is a standard testing method.
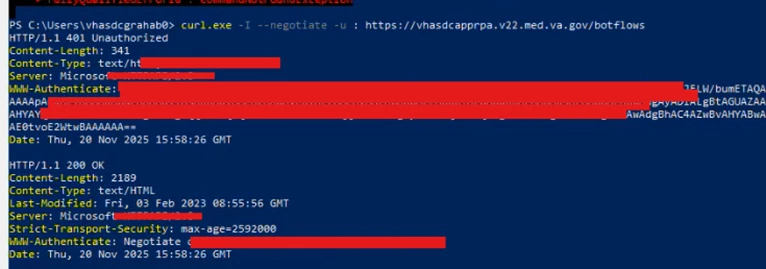
From the image above, you can see multiple handshakes. First, negotiate attempts to authenticate and sends the HTTP request.
The server responds with “unauthorized.” Curl then sends a second request with the actual credentials.
That second request receives a 200 OK response, which includes the response headers.
These are simply artifacts you can provide to your security team for their vulnerability checks. These are sanity checks, our application does use HSTS
Additional Information
If you still need more information, please email Support@nintex.com. We will be happy to assist you immediately.



