Security tests may cause K2 sites to be vulnerable to Clickjacking
kbt161441
PRODUCTIssue
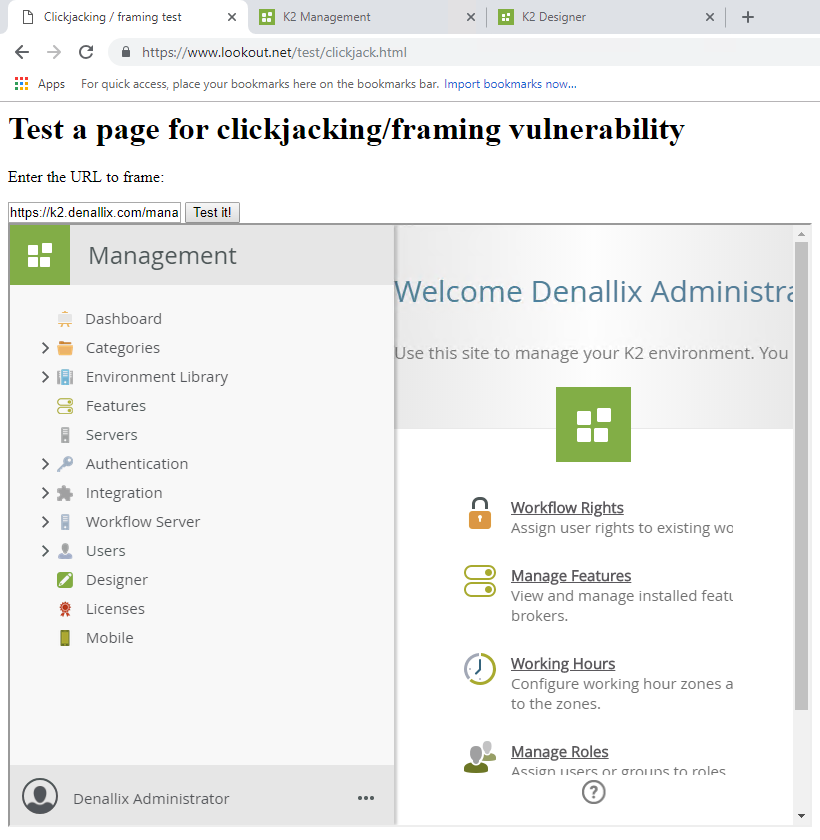
Security penetration tests conducted on a K2 environment may classify K2 sites to be vulnerable to clickjacking.
"Clickjacking is a malicious technique of tricking a user into clicking on something different from what the user perceives, thus potentially revealing confidential information or allowing others to take control of their computer while clicking on seemingly innocuous objects, including web pages". (source)
Symptoms
Troubleshooting Steps
Microsoft has an article published showing how this can be mitigated:
- Open the Internet Information Services (IIS) Manager.
- Expand Sites then select your K2 Site.
- Open HTTP Response Headers.
- Under the Actions pane, click Add.
- Add in the following header:
Name: X-Frame-Options
Value: SAMEORIGIN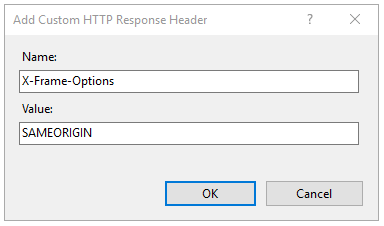
- Click on OK.
For environments integrated with SharePoint, please follow the steps below:
- Make a backup of the K2 smartforms Runtime web.config.
- Look for <customHeaders>.
- Under this section, add the following: <add name="Content-Security-Policy" value="frame-ancestors 'self' *.denallix.com portal.sharepoint.com" />In this example the K2 Smartforms Runtime site, all denallix.com SharePoint sites and the portal.sharepoint.com site would be allowed to host Smartforms in an iFrame.



