Issue
You want to use AAD and AD for Runtime sites
Solution
So we have a couple of options here, you can use AAD +/ AD to login to your Runtime sites
OR, you can create a secondary site for AAD and have a primary site for AD
1. To manually configure AAD for K2, you can use the following site (which is what I did) https://help.k2.com/onlinehelp/k2five/ICG/current/default.htm#Configure/SF/MultiAuthAAD.htm
2. Alternatively, if you have integrated K2 with SharePoint using the K2 for SharePoint app, in particular with a SharePoint Online tenancy or one that uses Azure Active Directory, you DO NOT need to do the configuration described here as it is done automatically during app installation and registration. This topic is specifically for environments that do not need SharePoint integration but need to integrate with AAD.
Step One:
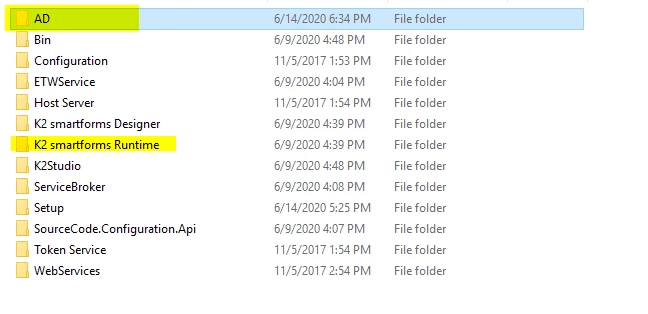
Copy the K2 Smartforms runtime folder and rename it to "AAD"
Step 2:
In your AAD Folder, go to the web.config file and edit it, look for the following line and ensure that you change it to match the realm that you will configure in K2 Management later on
<wsFederation passiveRedirectEnabled="false" issuer="http://none" realm="https://k2.denallix.com/aadusers/" requireHttps="false" />
Step 3:
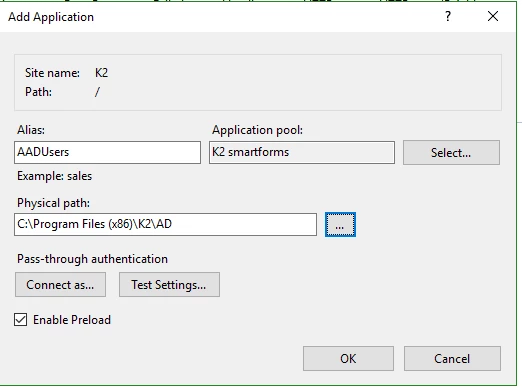
In IIS, right-click on your K2 Site and click "Add Application"
1. Enter the alias AADUsers
2. Select the Application pool to match your primary Runtime site (default should be K2 Smartforms - but could be different on your end.)
3. Specify the physical path to the directory created above
Step 4:
Go to K2 Management > Authentication > Claims > Realms and add a new realm to use AAD Issuer:

Now what will happen is that when my users hit:
https://k2.denallix.com/runtime/workspace - they'll be prompted to provide their windows credentials
https://k2.denallix.com/aadusers/workspace - they'll be prompted to provide their AAD Credentials

