HTTP Headers Exposing Sensitive Information
kbt144697
PRODUCTIssue
If you are performing penetration test on your SmartForms, you may encounter a warning about how the HTTP response headers returned contains information about the web server which could be useful to attackers.Symptoms
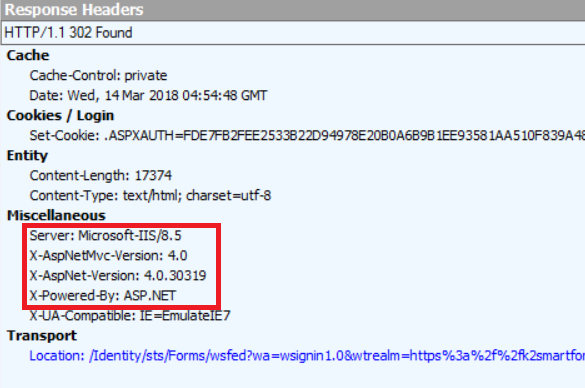
Penetration test report highlights the following HTTP headers that pose security issues:
- X-AspNet-Version
- X-AspNetMvc-Version
- X-Powered-By
- Server
Please note that these headers are not added by K2, but inserted automatically by IIS and .NET Framework.
To remove the X-AspNet-Version, X-AspNetMvc-Version, and Server headers:
- If you are using Forms STS for authentication, go to [Program Files]K2 blackpearlWebServicesIdentityStsForms.
- Alternatively, if you are using Windows STS, go to [Program Files]K2 blackpearlWebServicesIdentityStsWindows.
- Open Global.asax with a text editor
- Append the following line and save:
<script runat="server">
protected void Application_PreSendRequestHeaders(object sender, EventArgs e)
{
HttpContext.Current.Response.Headers.Remove("X-AspNet-Version");
HttpContext.Current.Response.Headers.Remove("X-AspNetMvc-Version");
HttpContext.Current.Response.Headers.Remove("Server");
}
</script>
To remove the X-Powered-By header:
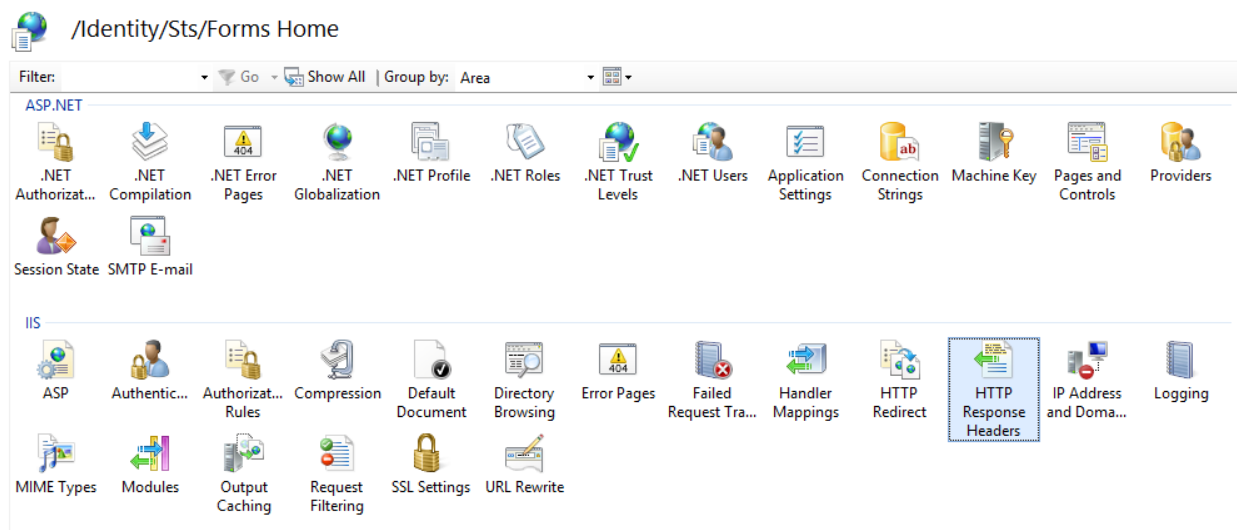
- Open IIS Manager
- Expand Sites > [Your K2 Site] > Identity > Sts
- Select Forms if you are using Forms STS for authentication. Otherwise, select Windows if you are using Windows STS.
- Select HTTP Response Headers
- Remove X-Powered-By:
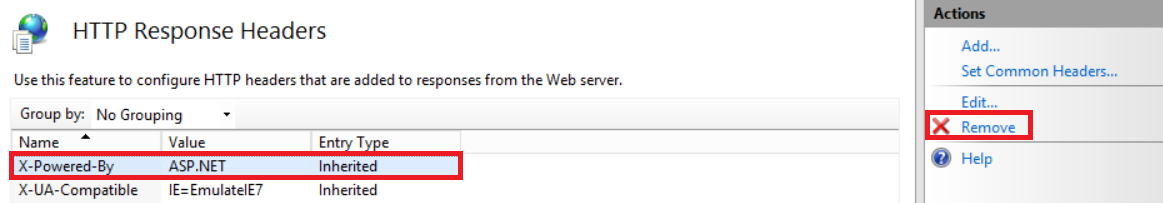
Once you are done, perform a IISRESET, clear browser cache, and check again if the headers appear.
]]> 7aa9901e-7d38-401e-9a3f-cd150b80d3cd Resolution Memo3

