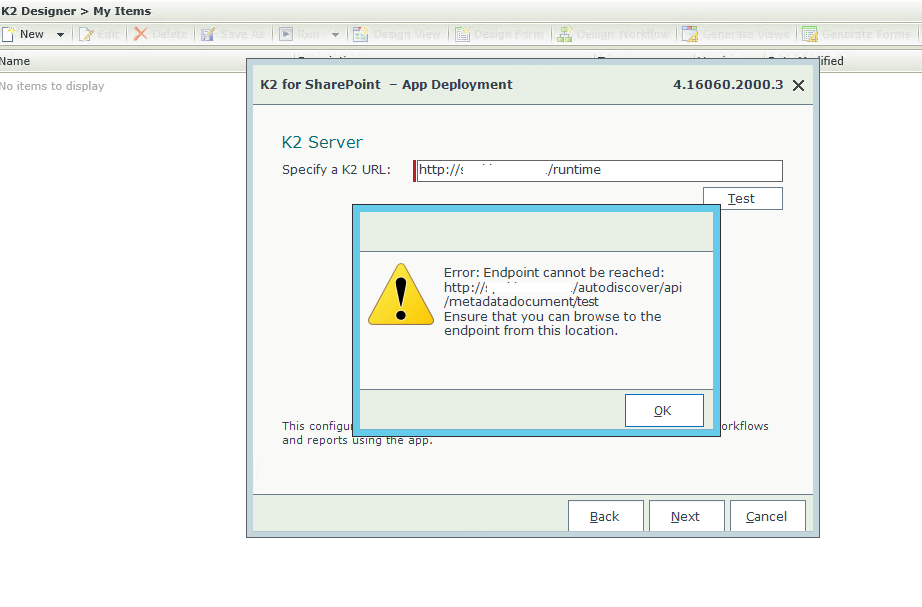
When trying to add the url on AppDeployment.exe, an error appears
kbt133539
PRODUCTIssue
When trying to access the url on App Deployment http://{ServerName}/autodiscover/api/metadatadocument/test, an error appears.Symptoms
When adding a URL to K2 for Sharepoint Activation it prompts the error below:
Ensure that you can browse to the endpoint from this location.
Resolution
To resolve this issue, please do the following:
- A full K2 database backup must be taken before you start.
- Also ensure that you the backup web.config file for workspace site - c:Program Files (x86)K2 BlackPearlWorkspacesiteweb.config
Steps to repair K2 OAuth
1. On the SharePoint Server, run the following PowerShell scripts as SharePoint Administrator:
• Remove-SPTrustedSecurityTokenIssuer -Id "K2 for SharePoint"
• Remove-SPTrustedRootAuthority -Id "K2 for SharePoint"
2. Then check to see that the Providers were deleted (there should be NO K2 High Auth Certificates for K2 for SharePoint)
• Get-SPTrustedSecurityTokenIssuer
• Get-SPTrustedRootAuthority
3. Then on the SQL server where the K2 DB is, run the following:
• DELETE FROM [K2].[HostServer].[Configuration] WHERE VariableToken like '[[]K2_SIGN%'
• TRUNCATE TABLE [K2].[Authorization].[OAuthAppOnlyToken]
4. Then run the following scripts to ensure it had been removed:
• SELECT * FROM [K2].[HostServer].[Configuration] WHERE VariableToken like '[[]K2_SIGN%'
• SELECT * FROM [K2].[Authorization].[OAuthAppOnlyToken]
5. Next, remove the K2 Certificate from the installation folder because you will be generating a new one:
• Program Files (x86)K2 blackpearlHost ServerBinOAuthCertificates
6. Run a K2 BlackPearl Reconfigure from installation Media (This is where you installed K2 Blackpearl from originally, remember to make a backup of the workspace config file.)
7. Check to see if a new Token and certificates were generated.
• Program Files (x86)K2 blackpearlHost ServerBinOAuthCertificates
• SELECT * FROM [K2].[HostServer].[Configuration] WHERE VariableToken like '[[]K2_SIGN%'
• SELECT * FROM [K2].[Authorization].[OAuthAppOnlyToken]
8. On the SharePoint Server as Farm Administrator, Run the AppDeployment.exe (remember that the user you run it as, has to have rights on the K2 DB to be able to retrieve the certificate).
Next, Run the AppDeployment.exe to added the K2 For Sharepoint application. After adding in the URL of K2 the issue should be resolved and K2 for SharePoint will be added as expected.


